When an account sits idle for an extended period, many services label it as dormant, a status that signals reduced access, higher scrutiny, or even temporary suspension. Reactivating such an account involves a careful dance between confirming your identity, clarifying ownership, and following security procedures set by the provider. The goal is not only to regain access but to restore trust between you and the service, ensuring that the account remains safe from unauthorized use while returning to its normal operational state. This article walks you through the steps, considerations, and practical approaches to bring a dormant account back to life, regardless of whether the account belongs to a bank, a social platform, an email service, or a corporate system.
Understanding the nature of dormancy and its implications
To reactivate effectively, you first need to understand what dormancy means within the specific ecosystem of your account. In financial contexts, dormancy can trigger regulatory alerts, stringent verification processes, and additional compliance checks designed to protect both the customer and the institution. In digital platforms, dormancy may translate to limited functionality, automatic lockouts after failed login attempts, or the concealment of certain features until identity is verified. The common thread across all contexts is the principle of security through verification: before access is restored, the system must be confident that the person requesting reactivation is indeed the legitimate owner.
Recognizing why dormancy was triggered helps you tailor your approach. A long period of inactivity can lead to password expiration, stale recovery options, or changes in contact information that you no longer control. Institutions routinely implement these measures to reduce risk, particularly if sensitive data or high-value assets are involved. By approaching the process with a clear understanding of the underlying security posture, you reduce the chance of extended outages, misunderstandings, or repeated verification cycles that can degrade the user experience. This awareness also helps you set reasonable expectations about timing, required documents, and potential fees or policy constraints that may apply in certain industries or jurisdictions.
Why reactivating matters for your everyday life
Reactivating a dormant account often unlocks access to essential services that support daily routines, financial management, and digital communication. In banking, regaining access may be crucial to manage funds, pay bills, or monitor transactions that could reveal fraudulent activity on your accounts. On social networks or email platforms, reactivation restores the ability to reconnect with contacts, retrieve important messages, and resume subscriptions or purchases you had scheduled. Even in enterprise environments, bringing a dormant employee or contractor account back online can restore collaboration, project workflows, and data continuity that teams rely on for productivity.
Beyond practical access, successful reactivation reinforces the message that you are an accountable user who values security. The process often includes updating contact preferences, strengthening passwords, enabling multi-factor authentication, and reviewing recent account activity to spot anything abnormal. When you approach reactivation as an opportunity to refresh security settings, you reduce the risk of future episodes of dormancy caused by outdated recovery options or weak credentials. This preventative mindset can lead to a more resilient account posture over time, making it harder for someone else to compromise your access in the future.
Preflight checks: what to gather before you start
Before you attempt reactivation, assemble a toolkit of information and documentation that may be requested during the process. This toolkit typically includes proof of identity such as government-issued IDs, a recent utility bill or bank statement showing your name and address, and information about the account itself like the username, last known login details, or associated email addresses. In many cases, you will also need to answer security questions or provide the answers you previously set up when the account was created. Keeping these materials organized in advance saves time and reduces the risk of errors that could trigger additional verification steps or temporary blocks.
Additionally, update any recovery channels connected to the account. That includes ensuring the recovery email address and phone number are current, accessible, and secure. If you no longer control a recovery email, you may need to arrange a new one and inform the provider of the change through the official channels. Having up-to-date contact points not only speeds up the reactivation but also helps you receive important alerts about suspicious activity, password changes, or security advisories that protect you after the account is back in service. This upfront preparation is a quiet investment that pays off when the reactivation workflow begins.
Identity verification and security considerations
Identity verification is the central pillar of reactivating a dormant account. Depending on the service, you may face a tiered process ranging from a simple one-time code delivered by email or SMS to a more rigorous check such as a live video call or submission of official documents. It is essential to be patient and methodical during this phase. Rushing through verification can lead to mistakes or miscommunications, which in turn cause delays or lockouts. When you are asked to present documents, ensure they are clear, legible, and match the information on the account. If any discrepancy arises, address it promptly and provide supporting evidence when possible.
Security hygiene plays a critical role after reactivation as well. Immediately after you regain access, review recent login activity, session histories, and connected devices. If you see a login from an unfamiliar location or device, report it to the provider and consider revoking access for those sessions. Strengthening your authentication approach can include enabling multi-factor authentication, using a dedicated authenticator app, and updating recovery options to prevent future dormancy triggers. A robust post-reactivation security routine reduces the risk of a relapse into dormancy and protects both your data and your money.
Documenting essential information for the reactivation process
Meticulous documentation reduces friction during reactivation and gives you a factual trail to reference if questions arise. Record details such as the account username, associated email addresses, phone numbers, responses to security prompts, and any reference numbers you receive from the support team. Keep a log of every contact you have with the provider, including dates, times, and the names of representatives you spoke with. If you are dealing with a financial institution, you may be asked to provide transaction history or account-specific identifiers; having a prepared set of dates and values can be a real time saver. Creating this repository not only speeds up the current process but also becomes a valuable resource for future account maintenance.
In parallel, ensure you have a clear understanding of the service’s terms around reactivation. Some platforms impose waiting periods, temporary usage restrictions, or additional verification for new devices. Knowing these constraints in advance enables you to plan your reentry with fewer surprises. If there are any fees associated with unfreezing an account or restoring certain features, you should understand the cost structure before initiating the process. Being well-informed helps you make decisions that align with your needs and expectations.
Choosing the right channel to initiate reactivation
Most dormant accounts can be reactivated through a combination of self-service portals, email communications, or direct telephone support. The right channel often depends on the sensitivity of the information involved and the level of verification required. Self-service portals can be convenient when the service supports account recovery tools such as password reset and identity checks that you can complete without human intervention. However, for more complex cases or where your identity is strongly tied to high-value assets, a live agent or a secure verification call may be necessary to confirm ownership and authorize reactivation.
When selecting a channel, consider the security posture of the method. Email-based recovery can be convenient but is vulnerable to phishing and email compromise; phone-based verification can be more direct but depends on the security of the phone line; in some cases, the best approach combines multiple channels to corroborate information. If you reach out via a social or publicly documented channel, you may be asked to continue through official channels rather than informal contacts for security reasons. A thoughtful choice of channel reduces frustration and increases the likelihood of a smooth reactivation experience.
Navigating self-service recovery tools
Self-service recovery options are designed to empower users to regain access without direct assistance. They typically include password resets, recovery link prompts, and identity verification steps that can be completed online. While convenient, these tools often have safeguards to prevent abuse, such as limiting the number of attempts within a given timeframe or requiring recent activity confirmations. If you encounter a hurdle, pause to review the prompts carefully, ensure you are using the correct account identifiers, and confirm you are following the official recovery flow rather than an unexpected redirect that could indicate a phishing attempt.
As you work through self-service tools, remember to keep your device secure. Ensure you are on a trusted network, avoid using public Wi-Fi for sensitive actions, and close any sessions once you complete the recovery steps. If the platform supports it, enable time-limited login codes or one-time passwords that expire quickly, so even if someone else gains access to your credentials, the window to misuse them is narrow. Self-service tools are powerful when used prudently; approached with caution, they can dramatically shorten the time to reactivation.
The reactivation workflow: what to expect
Reactivate a dormant account is rarely a single-click process. Expect a sequence that may involve verification of identity, confirmation of ownership of linked devices, reestablishment of recovery options, and a temporary reset of certain privileges while the system recalibrates your access level. Depending on the service, you might see a welcome notice, a notification about new terms of service you need to accept, or a security alert asking you to review activity within the last few months. It is normal for the process to feel gradual, with progressive unlocks as each layer of verification is completed successfully.
During this phase, it is important to monitor the process actively. If you receive alerts about suspicious activity, verify their authenticity and respond through official channels. If you experience delays, avoid rushing the process or providing information that is not requested. In some cases, a reactivation may require additional documentation or a follow-up verification attempt. Maintaining patience, keeping records of your interactions, and staying in contact with the support team will help you move forward without unnecessary setbacks.
Dealing with failed reactivation attempts and how to recover
Failures in the reactivation process can be disconcerting, but they are not uncommon. When a reactivation attempt fails, you should check whether the error stems from mismatched information, expired credentials, or a temporary system condition that requires a retry after a cooling-off period. If you suspect that your recovery options have become stale or compromised, take proactive steps to update them before attempting again. You may also request a different verification method, such as a secure video identity check or a manual review by a human agent, if the service offers it. Document each failed attempt and the reasons given to create a precise timeline for further escalation if needed.
In situations where you cannot regain access through standard channels, it can be valuable to seek guidance from a senior support representative or a dedicated recovery team. They can review unusual account activity, confirm ownership through additional proofs, and propose steps that align with regulatory requirements or internal policy mandates. While this path may take longer, it often yields a clearer path to resolution and reduces the risk of repeated, unsuccessful attempts that could trigger security holds or extended restrictions.
Post-reactivation: securing and stabilizing the account
Once access is restored, your immediate focus should shift to securing the account and stabilizing its operations. This includes updating your password to a strong, unique credential, enabling multi-factor authentication, and reviewing the list of connected devices and active sessions. Revoke access for any devices or sessions that you do not recognize or that appear suspicious. Turn on alerts for critical activities such as password changes, new device sign-ins, or changes to recovery information. A proactive security stance after reactivation helps prevent a recurrence of dormancy or other security incidents that could jeopardize the account again in the future.
Additionally, reestablishing a sustainable activity pattern is important to prevent future dormancy. Set reminders or adopt habits that keep your account in regular use, such as monthly logins, scheduled payments, or periodic reviews of account activity. Consider updating preferences for notifications so that you remain informed about important events without being overwhelmed by alerts. For accounts tied to financial assets, consider setting up time-bound review routines that ensure you monitor balances, transactions, and any unusual adjustments on a routine basis. Creating this rhythm after reactivation helps maintain account vitality and reduces the chances of slipping back into dormancy.
Security pitfalls to avoid during reactivation
During reactivation, be mindful of phishing and social engineering attempts that mimic official communications. Always verify the sender, the URL, and the contact method through official channels. Do not disclose sensitive information in unsecured messages or on platforms that do not show strong indicators of legitimacy. If a request asks you to bypass standard security steps, pause and consult the official help resources before proceeding. Remember that legitimate reactivation processes rarely require you to reveal sensitive data in insecure environments or to grant access to third-party applications you do not recognize.
In addition, avoid reusing compromised passwords or reactivating accounts on devices that may have malware. Run a security check on your devices, update software, and make sure your antivirus or endpoint protection is current. If you use password managers, update the vault with the new credentials and ensure synchronization across devices remains seamless but secure. These precautions create a safer foundation for the reactivated account and reduce the risk of repeating the cycle of dormancy due to credential compromise or device-related threats.
Maintaining a healthy account posture to prevent future dormancy
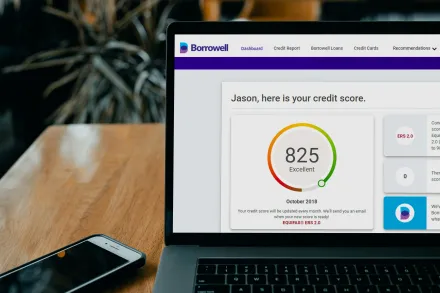
Prevention is more effective than reactive security. After reactivation, establish a routine that helps keep your account lively and well-protected. Regular checks of login history, device authorizations, and recovery options are essential. Consider enabling device recognition features that reduce friction during sign-ins while preserving strong security. Scheduling periodic reviews of linked apps, permissions, and integrations helps ensure that only trusted tools remain connected to your account. If a service offers account activity dashboards or security score indicators, use them to gauge your risk profile and adjust settings accordingly.
Another key habit is to keep contact details updated. If your email or phone number changes, update them promptly and verify that recovery channels are accessible. This is particularly important for accounts that hold sensitive information or grant access to financial services. By maintaining current contact channels, you improve your ability to respond quickly to security alerts and prevent unnecessary blocks that could trigger dormancy in the future. A well-maintained account is less likely to drift into a dormant state and easier to reactivate if needed again later.
Common mistakes and how to avoid them during reactivation
Many reactivation attempts stumble because users misread instructions, hurry through verification steps, or fail to keep records. A common mistake is failing to confirm ownership of linked devices or email addresses, which can stall the process and necessitate repeated verification cycles. Another frequent pitfall is not updating recovery options prior to initiating reactivation, which can create a bottleneck if the system needs to send codes or prompts. Avoid these issues by taking a deliberate, organized approach, double-checking every field, and ensuring that you provide accurate information that matches the account records.
Do not underestimate the importance of timing. Some accounts have limits on how frequently you can attempt reactivation or how often you can request a password reset within a given window. If you exhaust these limits, you may be forced to wait before trying again, potentially extending the downtime. By pacing your requests and honoring the service’s guidelines, you reduce the risk of triggering security holds that complicate the reactivation and can harm your long-term access. Patience, coupled with thorough preparation and careful communication, tends to yield the best outcomes in complex reactivation scenarios.
Real-world scenarios: stories of successful reactivation
In many cases, reactivating a dormant account is less about dramatic measures and more about methodical steps and clear communication. Consider a scenario where a longtime banking customer finds their online banking profile locked due to inactivity, but their identity remains consistent with existing records. By contacting the bank with a prepared set of identity proofs, verified recent activity, and updated contact information, they are guided through a streamlined verification process. The bank may temporarily restrict certain features during the reactivation, but access to essential services is restored after confirming ownership, and the customer can resume bill payments and balance monitoring without significant disruption.
Another example involves a personal email account that has remained dormant for several years. The owner initiates recovery through the provider’s self-service portal, then follows up with a brief call to confirm identity and respond to a security question. After successful verification, the account is reactivated, and the owner updates the recovery phone number and email. Within hours, the person is back in control, regaining access to saved messages, important communications, and subscription services that rely on their email address. These narratives demonstrate how a disciplined approach, leveraging available verification channels and keeping documentation handy, can turn dormancy into a resolved issue rather than a prolonged problem.
There are also organizational examples where a dormant employee account is reactivated to restore collaboration across teams. In such cases, administrators align identity verification with internal controls, confirm role assignments, and reestablish access to shared drives and project tools. The process emphasizes least privilege and timely revocation of any stale entitlements. When handled with care, these reactivations reconstitute workflows, minimize downtime, and reinforce the organization's commitment to secure, reliable access management. Across individual and corporate scenarios, the underlying pattern remains consistent: thorough preparation, prudent verification, and vigilant security practices lead to durable reactivation outcomes.
Final reflections on reactivating a dormant account
Reactivating a dormant account is ultimately about reestablishing a trusted bridge between you and a service. It requires patience, a clear plan, and attention to security. The best outcomes come from moving deliberately through identity verification, updating recovery options, and adopting strong post-reactivation safeguards. By treating the process as an opportunity to refresh your credentials, review your security posture, and reengage with the service on your own terms, you create a durable path back to normal operations. Remember that every provider has its own policies, timelines, and requirements, but the core principles of ownership verification, secure access restoration, and proactive account maintenance apply across the board, enabling a smoother, safer reactivation experience for nearly any dormant account.










