Foundations and motivation
In the rapidly evolving landscape of decentralized systems, two broad approaches have emerged as leading methods for achieving consensus among distributed participants: proof of work and proof of stake. These terms describe distinct ways in which a network of nodes agrees on the state of a shared ledger, validates transactions, and prevents double spending and conflicting histories. The motivations behind these mechanisms are not solely technical; they arise from a balance of security guarantees, energy considerations, incentive structures, and long term resilience against a variety of threats. To understand how these mechanisms compare, it helps to start with a mental model of what makes a distributed system trustworthy when no central authority exists. In such a setting, trust is not placed in a single participant but in a process that, nonetheless, can be audited, verified, and replicated by honest actors. Proof of work and proof of stake each propose a way to allocate power to participants in proportion to the resources they contribute or the stake they hold, with the network's rules enforcing the outcomes over time. This framing leads to a broader discussion about how material costs, risk, and incentives interact to shape behaviors within the network and, ultimately, its security posture.
Definition: what is proof of work
Proof of work is a mechanism in which participants, typically called miners, compete by performing computational work that is expensive to produce but easy to verify. The work in this context takes the form of solving cryptographic puzzles that require substantial processing power and energy input. In most practical deployments, the outcome of this contest is a new block of transactions that is then appended to the blockchain, and the miner who solves the puzzle first is rewarded with new coins and, perhaps, transaction fees. The security premise rests on the idea that an attacker would need to control a majority of the network's computational power to rewrite history, a feat that becomes progressively more costly as the network grows and as more miners join with more capable hardware. The irreversibility of blocks in proof of work comes from the cumulative difficulty and the requirement to outpace the rest of the network in producing the longest valid chain, a property that honest work, when funded by genuine economic incentives, tends to reinforce over time.
Within a proof of work system, the energy cost of producing a valid block is not merely a side effect but a central component of the economic model. Security becomes a function of energy expenditure and equipment investment, and the network thereby inherits a kind of physical barrier to attacks that is difficult to replicate through purely software changes. The difficulty adjustment mechanism is carefully designed so that blocks are produced at a predictable cadence under typical conditions, while the system remains robust to fluctuations in available hashing power. The resulting alignment between investment in hardware and the rate at which new blocks appear is a cornerstone of the mechanism’s resilience, though it also highlights the environmental concerns and the potential for centralization enabled by economies of scale in mining operations.
Core principles of proof of stake
In contrast, proof of stake centers the distribution of influence on the network around the size of participants’ stake and their long term commitment rather than the immediate expenditure of computing resources. In a proof of stake system, validators lock up a portion of their native tokens as stake, which serves as collateral that can be slashed if they behave dishonestly or negligently. Validators are selected to propose and attest to new blocks in a way that depends on their stake and other elements such as randomness and protocol-defined penalties. The core security claim here is that the risk of long term losses due to misbehavior discourages misbehavior more effectively than the promise of short term rewards, because the stakes involved can be substantial and are held over time. Finality in proof of stake systems often requires a series of attestations and a threshold of validator consensus before a block becomes irrevocably part of the canonical history, a property that aims to dramatically reduce the risk of reorganization after blocks have been confirmed. In this model, the energy cost is typically much lower than in proof of work, since the network’s security does not depend on continuously burning electricity to outpace a competitor. Instead, the security layout relies on economic discipline, honest behavior reinforced by penalties, and the ability to assert finality as stake becomes more entrenched through time and consistent participation.
Formally, proof of stake reframes the ledger’s safety from a race to burn resources into a race to preserve value through responsible stewardship of stake and protocol rules. Participation depends on ownership of the asset and on proper governance, which introduces a different set of incentives and potential centralization concerns. The emphasis on long term economic commitments has driven experiments with reward schemes, slashing rules, and validator rotation that collectively shape how the network evolves, how new participants join, and how decisions about upgrades and parameter changes are made. The result is a different flavor of security that is intimately tied to the economic environment surrounding the asset, the degree of decentralization among validators, and the reliability of the underlying governance mechanisms that govern accountability and dispute resolution.
Economic incentives and security models
Both proof of work and proof of stake are rooted in incentive compatibility, yet they translate this principle through fundamentally different channels. In proof of work, security incentives are anchored in the correlation between energy expenditure and block creation probability. Miners invest capital in hardware, electricity contracts, and operational facilities with the expectation that honest mining will yield a return as the network rewards consistent block production and fees. The ubiquitous assumption is that the majority of the network’s hash power remains honest, because collusion or attack would require overwhelming control of hash rate to rewrite history, which would come at an enormous cost and likely reduce the value of the attacker’s own holdings. The incentive structure thus aligns with the broader market dynamics around the currency’s price, mining revenue, and the relative cost of electricity and equipment upgrades, creating a dynamic feedback loop that has preserved the security of long-running proof of work networks despite periodic concentration in mining operations.
In proof of stake, incentives revolve around stake itself and the penalties associated with dishonest behavior. Validators stand to gain as the network grows and as rewards accumulate through participation and the processing of transactions, but they also risk losing stake if they engage in activities that undermine consensus, such as equivocation, long-range attacks, or misreporting. Slashing conditions are designed to create a strong deterrent against misbehavior, and the eventual outcomes are intended to be more predictable and energy efficient than their proof of work counterparts. The economic model emphasizes stake accumulation, network participation, and transparent governance, while also depending on the ability of the protocol to detect and mitigate misbehavior in a timely and robust fashion. The long horizon of staked value fosters a different kind of security commitment, one that rewards patience and depends on the integrity of the validator set, the quality of the governance processes, and the resilience of the incentive mechanisms against emerging threats and market dynamics.
Both systems face tradeoffs between resilience, centralization risk, and adaptability to changing conditions. Proof of work can be highly resilient to short term economic shocks because mining power can shift geographically and across participants, adding a layer of distribution but potentially concentrating influence in major mining hubs. Proof of stake can enhance energy efficiency and potentially speed up finality, but it raises questions about stake distribution, validator incentives, and the possibility of governance capture by well-capitalized participants. Each model thus embodies a different philosophy of how to balance openness, security, and sustainability as a blockchain network matures and confronts evolving technological and economic landscapes.
Attack vectors and resilience
Security threats in proof of work networks primarily include the possibility of a 51 percent attack, where a single actor or coalition commandeers the majority of hash power to rewrite history or prevent other miners from producing blocks. While this scenario is not trivial to achieve and becomes more difficult as the network grows, the magnitude of its economic and environmental cost remains a key consideration. Attacks could also stem from sudden changes in energy markets, hardware shortages, or strategic concentration of mining power in jurisdictions with fewer regulatory safeguards. The defense against such risks rests on the network’s incentive alignment, the diversity of miners, and the ever-present need to maintain a robust and distributed infrastructure that remains accessible to new entrants. In practice, successful long term attacks against large proof of work networks have proven difficult because the sheer scale required often means a self-defeating economic calculation for the attacker, as the same incentives that sustain the honest network would also erode the attacker’s own asset value if block rewards and network usage decline.
Proof of stake introduces a different set of resilience considerations. The risk model emphasizes the possibility of long-range attacks, where the attacker attempts to reconstruct a history by leveraging old private keys or outdated states. To mitigate such threats, protocols implement epochs, reward schedules, and finality checkpoints that reduce the feasibility and payoff of trying to rewrite history after significant time has passed. Slashing penalties serve to deter validators from acting against the protocol’s integrity, but these measures must thread the needle between being harsh enough to deter misbehavior and fair enough to avoid suppressing participation. Additionally, the validator electorate is exposed to concentration risks wherein a handful of stakeholders control a large portion of the stake, potentially translating into political influence that can sway governance decisions or upgrade paths. Throughout, the ability of the protocol to rapidly detect and respond to anomalies, while preserving user confidence in safety and predictability, is a decisive determinant of resilience for proof of stake networks alike.
Environmental and energy considerations
Environmental impact has become a salient lens for evaluating proof of work networks. The energy-intensive nature of competitive mining is a fundamental characteristic of PoW and is often cited by critics as a reason to favor alternative consensus mechanisms. Proponents argue that the energy expenditure corresponds to real-world economic activity and aligns with tangible hardware utilization and grid dynamics, potentially enabling incentives for cheap energy and hardware recycling. Critics emphasize the risk of inefficiency, energy waste, and the difficulty of measuring the opportunity cost of resources that could be allocated to other productive uses. In response, many PoW networks have seen changes in mining location, the adoption of renewable energy, and the emergence of mining that coexists with energy markets in a way that mitigates environmental impact while preserving security guarantees.
Proof of stake presents a different environmental profile. Since consensus is not driven by continuous hashing races, the energy footprint tends to be substantially lower. The absence of a perpetual energy arms race means that security is not tied to the price of electricity or the availability of cheap power. Instead, the focus shifts to the economic and governance aspects of stake and validator operations. The sustainability narrative around PoS often highlights the ability to maintain secure networks with minimal energy consumption, enabling broader participation and reducing the externalities associated with large-scale mining. This shift has resonated with proponents who seek to align blockchain infrastructure with wider climate and sustainability goals while preserving the ability to scale and evolve with user needs and technological progress.
Centralization concerns
Both consensus models face centralization challenges, though of different flavors. In proof of work, centralization tends to manifest through concentration of hash power in a few large mining pools, specialized equipment, and geographical hubs with favorable energy and regulatory environments. This concentration can transfer influence away from individual users, potentially affecting governance and the distribution of block rewards. Mitigations commonly discussed include encouraging decentralization through incentives that reward smaller participants, improving hardware accessibility, and designing networks that resist single-point failure modes. The social and political dimensions of mining power, including regulatory responses and public perception, also influence how centralized or dispersed the ecosystem remains over time.
In proof of stake, centralization risks arise primarily from wealth concentration and governance dynamics. When a large fraction of stake sits with a relatively small cadre of entities, those actors can exert disproportionate influence over protocol upgrades, parameter changes, and the direction of development. To counteract these risks, researchers and practitioners explore ideas such as distributed validator sets, evolution of slashing rules, and careful design of reward schemas that encourage broad participation. The social contract inherent in PoS networks emphasizes transparency, predictable governance, and robust mechanisms for accountability, while recognizing that unequal distribution of stake can create practical obstacles to universal participation and fair representation. The balance between inclusive participation and network stability thus becomes a persistent topic of discussion as networks evolve toward broader adoption and more complex governance processes.
Hybrid and other variants
Beyond the pure dichotomy of PoW and PoS, a variety of hybrid and peripheral approaches have emerged in the landscape of blockchain consensus. Some designs incorporate elements of proof of work with proof of stake to gain advantages from both models, sometimes using PoW to bootstrap security and PoS to finalize blocks once a critical mass of stake accrues. Other approaches lean on delegated mechanisms, where token holders elect a smaller group of validators who perform the heavy lifting of block production and finalization, while ordinary users retain influence through governance rights. There are also algorithmic innovations that draw on proof of authority, which relies on trusted validators with reputational credentials, and other mechanisms that emphasize fast finality, censorship resistance, or highly efficient consensus. While these variants stretch the taxonomy, they are unified by the common aim of delivering secure, scalable, and user-friendly distributed systems that can adapt to a broad spectrum of applications and risk tolerances. The practical choice among them often reflects the intended use case, regulatory considerations, and the ecosystem’s appetite for complexity, decentralization, and governance resilience.
In practice, many networks experiment with scheduled upgrades and phased transitions that allow the community to observe behavior under stress, test finality properties, and calibrate incentives for participants to act in alignment with long term network health. The resulting landscape is a tapestry of technical decisions and social processes that shape how quickly a project can adapt to new threats, how it can scale to handle growing transaction volumes, and how it manages the tradeoffs between speed, security, and energy efficiency. Such hybrid arrangements illustrate that consensus design is not a single binary choice but a spectrum where networks may shift over time in response to external pressures, technological breakthroughs, and evolving user expectations.
Economic models and network security
To understand the long term security of a blockchain, one must examine not only the immediate mechanics of block formation but also the expectations about how rewards accrue, how costs scale, and how the distribution of influence evolves. In proof of work, security is reinforced by the fact that attackers would need to outspend honest participants to alter the ledger, a dynamic that tends to increase with the value of the network and the cost of acquiring specialized hardware. The incentive to maintain mining operations and sustain the network often emerges from the expectation that the currency will appreciate, thus rewarding the capital invested in mining infrastructure and electricity contracts. However, the energy and equipment cost could also render the system more vulnerable to external shocks, trade restrictions, or strategic shifts in energy markets that alter the relative profitability of honest participation versus malicious activity.
In proof of stake, security is anchored to the value of the stake and the costs associated with misbehavior. The principle is that the economic consequence of losing stake or facing penalties outweighs the potential gains from attacking the network. Because stake is often liquid and tradable, the shifts in market value can influence the level of commitment participants have to the protocol’s integrity. The mechanism of slashing creates a powerful deterrent against strategies that could undermine consensus, but it also raises concerns about the clarity of rules, the fairness of enforcement, and the potential for disputes where the line between a misstep and a malicious act might be nuanced. The distribution of stake and the transparency of validator activity thus play a central role in the perceived and actual security of a PoS network. Consequently, ongoing research and development focus on strengthening the accountability framework, clarifying governance paths, and building systems that remain resilient in the face of sophisticated adversaries while maintaining broad accessibility and fair opportunity for ordinary users to participate as validators or delegators.
Real-world examples and case studies
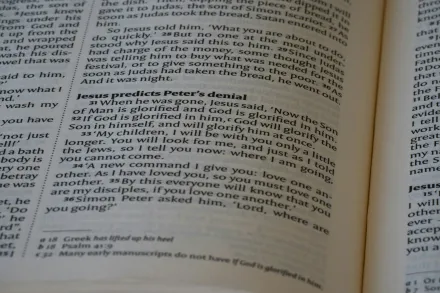
The narrative of proof of work is closely tied to early and enduring networks that champion the idea of mining as an open invitation for anyone with computational resources to participate. Bitcoin remains the quintessential PoW network, a symbol of decentralized financial experimentation that has persisted for over a decade and a half. Its security and resilience derive from a long history of large-scale participation, global distribution, and a robust incentive structure that has shown remarkable endurance in the face of varying price pressures, regulatory noise, and technological shifts. Ethereum, initially a PoW network, embarked on a major transition by moving to a proof of stake consensus model in a landmark upgrade sometimes referred to as the merge. The transition aimed to reduce energy intensity, shift toward a governance model that emphasizes stake-based participation, and unlock new capabilities such as improved scalability through subsequent upgrades. The post-merge reality has included ongoing optimization of validator responsibilities, enhancements to finality guarantees, and continuous experimentation with shard-like architectures to increase throughput while preserving security assurances handed down from the PoS model. These real world examples illustrate how a network’s choice of consensus mechanism can cascade into technical upgrades, economic dynamics, and governance practices that shape the long-term trajectory of the ecosystem.
Beyond these prominent cases, a diverse set of projects explores variants and novel approaches. Some networks experiment with permissioned or semi-permissioned validator sets to achieve predictable performance in enterprise contexts, while others pursue hybrid designs intended to offer immediate finality with gradual decentralization. The broader industry narrative reflects a growing recognition that no single mechanism is a silver bullet; rather, the choice of consensus structure interacts with the protocol’s goals, the expected user base, and the willingness of participants to engage with the system’s governance and economic layers. As more networks reveal their experiences through real-world operation, practitioners gain insights into how best to balance security, efficiency, accessibility, and resilience in the face of evolving threats and opportunities.
Implementation challenges and roadmap
For proof of work, the practical engineering challenges include maintaining hardware diversity, ensuring the reliability and scalability of mining operations, and defending against evolving hardware-level attacks or supply chain constraints that could affect access to mining components. The roadmap often involves exploring improvements in energy efficiency, evolving consensus parameters to adapt to changing block production rates, and integrating better on-chain data structures to support higher transaction throughput. The complexity of coordinating a global network of independent miners, each subject to local conditions and policies, makes the design of upgrade mechanisms and governance processes particularly intricate. The evolution of PoW networks thus hinges on fostering a healthy ecosystem where new entrants can participate, existing participants have confidence in the rules, and the system remains robust under stress from market cycles and regulatory developments.
For proof of stake, the implementation agenda centers on ensuring robust validator onboarding, secure key management, and reliable slashing and incentive schemes that deter misbehavior while minimizing false positives. Another critical area is the development of finality mechanisms, which are essential to establishing when a block or a chain of blocks can be considered irreversible. The protocol must also handle validator churn, ensuring that validator sets can adapt to changing participation levels without sacrificing security or performance. Governance processes require transparent upgrades, clear parameter definitions, and mechanisms to resolve disputes that arise from disagreements among stakeholders. The roadmap frequently includes performance optimizations, upgrades to cross-chain interoperability, and the gradual introduction of more sophisticated incentives to distribute participation more evenly across the network. Taken together, these elements form the backbone of a pragmatic plan for advancing PoS networks from concept to widespread, dependable operation while continuing to address edge cases and emergent behavior in the wild.
Future directions and ongoing research
The frontier of consensus research is marked by questions about scalability without sacrificing security, the degree to which finality can be accelerated through more refined cryptographic proofs, and how cross-chain communication can be achieved with trustless assurances. In proof of work, researchers continue to explore optimization strategies that reduce energy consumption without undermining the protective properties offered by distributed hashing power. In proof of stake, attention focuses on reducing centralization risks by designing reward and penalty systems that encourage broader participation, ensuring robust validator election and rotation mechanisms, and exploring governance frameworks that strike a fair balance between investor influence and community-driven decision making. The evolving research agenda also considers the implications of quantum resistance, the impact of regulatory frameworks on network design choices, and the social dimensions of participation that determine whether users perceive the system as fair, inclusive, and trustworthy. As the landscape broadens, developers and researchers work together to create modular, adaptable architectures that can accommodate emerging use cases, including privacy-preserving transactions, programmable smart contracts, and scalable data availability solutions, all while preserving the fundamental guarantees that users expect from a secure, decentralized ledger.
In sum, understanding the distinctions between proof of work and proof of stake requires looking beyond the surface level of who wins in block races or who gets the right to validate transactions. It calls for a holistic view that considers how resource commitments translate into economic incentives, governance capabilities, and technical guarantees under a spectrum of environmental and regulatory conditions. The choice of consensus is not merely a technical preference but a strategic decision that influences the network’s fate, its participants, and the kinds of applications it can sustain over the long arc of its development. As new ideas emerge and communities experiment with different configurations, the underlying questions remain: how can systems achieve broad participation, how can they remain secure against a wide range of adversaries, and how can they do so in a way that is sustainable, transparent, and adaptable to the evolving needs of users around the world?